The digital landscape is constantly evolving, with threats and vulnerabilities surfacing at an unprecedented rate. Among these are 0day vulnerabilities, which pose significant risks to cybersecurity. One intriguing aspect of the underground community is the 0day onion, a marketplace and distribution channel for these exploits. This article delves into the workings of the 0day onion and its implications for both attackers and defenders in the realm of cybersecurity.
What is 0day Onion?
The economic model for such a exploit broker is predicated on the extreme value a buyer places on deanonymizing targets who have specifically chosen Tor for its strong privacy guarantees. This process, analogous to peeling an onion, obscures the origin of the traffic, making it exceptionally difficult to trace back to the individual. The value of a 0day is intrinsically linked to its novelty and the potential damage it can inflict, making it a highly sought-after commodity on both legitimate and illicit markets. The term signifies that developers have had zero days to address the problem since its discovery, leaving systems exposed. The exploit is deployed silently, ideally without triggering any alarms, to establish a persistent presence on the target systems.
Rapid7, creators of the Metasploit Framework, have a searchable CVE database on its website. Known for both its bite and excellent storage capabilities (half a year or more) Red Creole is the perfect onion to use in spicy Cajun dishes. If cutting onions tends to make you tear up, this is the variety for you. However, there’s a chance you may run into illegal activity on all but the best onion sites.
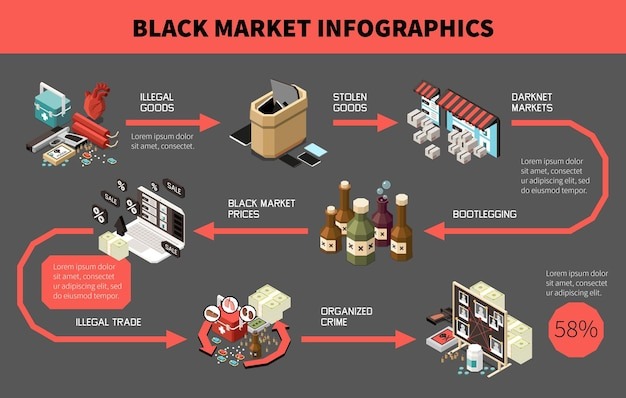
The 0day onion refers to a specific segment within the dark web, where zero-day vulnerabilities are bought, sold, and traded. A zero-day vulnerability is a flaw in software or hardware that is unknown to the vendor and, consequently, lacks a patch. The 0day onion allows cybercriminals to access and exploit these vulnerabilities before they are discovered and mitigated, making it a high-stakes environment.
The Mechanics of 0day Onion Markets
Within the 0day onion platform, sellers often post detailed descriptions of the vulnerabilities, including potential impacts and exploitation methods. Buyers range from individual hackers seeking to enhance their toolkit to organized cybercriminal groups looking to exploit these vulnerabilities for profit. The transactions typically occur using cryptocurrencies to maintain anonymity, aligning with the principles of the darknet.
Impacts of the 0day Onion
The proliferation of 0day vulnerabilities available through 0day onion markets poses a dual threat. On one hand, these vulnerabilities can be used in targeted attacks against corporations and governments, leading to data breaches and financial losses. On the other hand, they also drive innovation in defensive cybersecurity measures, as organizations strive to fortify their systems against these unseen threats.
Ethical Considerations
- As someone who just want strong privacy, I see hidden services as problematic neighbors and I would be glad to see them go.
- As a result, the security landscape around 0day onion services requires continuous monitoring, threat intelligence sharing, and proactive security measures.
- Within this community, anonymity is key; many users rely on the Tor network to remain hidden while they access sensitive information related to malware and data breaches.
- In the realm of cybersecurity, the world of 0day onion sites presents unique risks that are often overlooked by individuals exploring the darknet.
- Marketplaces offering stolen data, contraband, drugs, and hacking services operate within these hidden spaces.
- Below are some affordable, quality gardening gifts that will have… No matter where you’re growing or what you’re cooking, there’s an onion for you.
While the 0day onion serves as a hub for malicious activity, it raises important ethical questions within the cybersecurity community. Some argue that responsible disclosure—where researchers inform the vendor of a vulnerability before it is publicly disclosed—should be the norm. However, the existence of the 0day onion seems to undermine this idea, encouraging a culture where vulnerabilities are hoarded and weaponized.
Staying Safe from 0day Exploits
Organizations and individuals must be proactive in their cybersecurity measures to mitigate the risks posed by 0day vulnerabilities available on the 0day onion. Regular software updates, robust security protocols, and comprehensive threat intelligence are crucial in defending against these risks. Investing in training and awareness programs can empower individuals to recognize potential threats before they can be exploited.
The Future of 0day Vulnerabilities
As technology continues to advance, the 0day onion market is likely to expand, presenting ever-evolving challenges for cybersecurity. With the rise of artificial intelligence and the Internet of Things, the number of potential vulnerabilities will only increase, leading to a growing demand for zero-day exploits. This developing landscape necessitates continuous adaptation and vigilance from cybersecurity professionals to safeguard their systems from these hidden dangers.
In summary, the 0day onion represents a significant challenge in the world of cybersecurity. It embodies the fine line that exists between innovation and exploitation, emphasizing the need for ongoing dialogue and efforts to secure our digital environments.