The dark web is a part of the internet that isn’t indexed by traditional search engines. It offers anonymity and privacy, often attracting users who want to access content that may be unavailable or restricted on the surface web. However, navigating the dark web can be fraught with risks, so understanding how to access it safely is essential. This article provides a comprehensive guide to accessing the dark web while emphasizing security and legality.
Lesser known darknets include ZeroNet, a peer-to-peer-based web hosting model developed in 2015 that doesn’t use IP addresses or domains for websites. The multi-layered encryption gives anonymity to its users and service providers alike. Tor operates almost like a traditional web browser; you can download it to your machine and use it to access different sites.
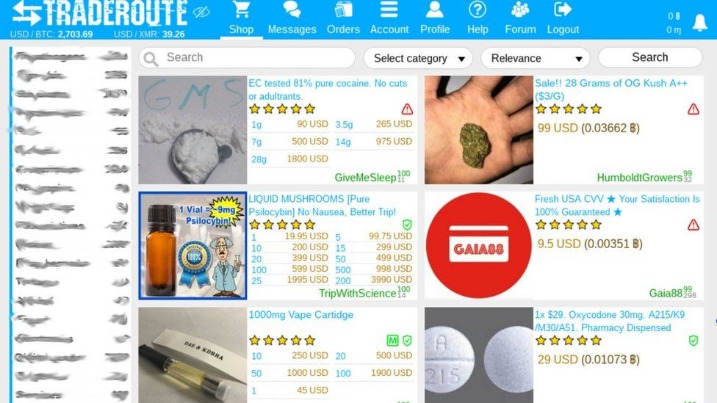
Nonetheless, the dark web does have a well-earned reputation for illegal content and activity taking place within it. Although, this depends on the country you’re in, as totalitarian regimes are obviously against platforms that provide anonymity to users. To keep your online activities private, the Dark Web uses advanced encryption, different from what you use every day.
CrowdStrike Falcon® Adversary Intelligence provides comprehensive monitoring of the deep and dark web to identify threats targeting an organization’s brand, employees, and data. When accessing the dark web, you can only use a secure browser (which is also called an onion browser). This includes websites, blogs, online product listings, and even public posts on social media. The surface web, which is also called the visible web and the open web, is any website that search engines can add to their database. This includes websites that gate their content behind paywalls, password-protected websites, and even the contents of your email.
Accessing The Dark Web
To start accessing the dark web, users typically rely on specialized software. Below are the key steps to get started:
Step-by-Step Guide
- As the dark web continues to grow, safe access to dark web sites matters more than ever.
- A comprehensive cybersecurity monitoring solution should include surveillance of the deep and dark web, both of which may play host to cyberattack infrastructure.
- Generally legal content with controlled access
- This information can help mitigate cyberthreats before they are committed or be used to recover leaked data from a breach.
- The dark net is not quite as lucrative as it used to be and the prices for most of these items or services have gone down in recent years.
- Download the Tor Browser: The most common way to access the dark web is through the Tor network. Download the Tor Browser from its official website to ensure you’re getting a legitimate version.
- Install the Browser: Follow the installation instructions carefully. It’s a straightforward process, but ensure you are not exposing yourself to potential malware.
- Configure Your Settings: Set your security level within the Tor Browser. For most users, the default settings provide adequate protection, but adjust them according to your comfort level.
- Navigate to .onion Sites: The dark web features websites with .onion domains. Use trusted directories to find links to these sites, as many can be unsafe or illegal to access.
Safety Tips for Accessing the Dark Web
While accessing the dark web can be tempting, it is crucial to prioritize your safety and privacy. Here are some tips:
- Be Cautious: Many sites on the dark web host illegal content. Always understand the legality of what you're accessing.
- Use a VPN: Pairing Tor with a reliable Virtual Private Network (VPN) adds an additional layer of privacy.
- Keep Personal Information Private: Avoid using your real name, email, and other identifiable information on the dark web.
- Disable Scripts: Many dark web sites use JavaScript, which can compromise your security. Adjust your browser settings accordingly.
Frequently Asked Questions (FAQs)
1. What is the difference between the deep web and the dark web?
- Some browsers load active scripts that hidden services use to test for weaknesses.
- The Deep Web thus balances safeguarding data with the practicalities of access, a dynamic critical to modern digital operations.
- Tor66 blends a traditional search engine with a categorized directory of onion sites.
- These threats make it important to rely on updated privacy tools rather than outdated browsers or casual browsing habits.
The deep web comprises parts of the internet not indexed by standard search engines, which includes databases, private corporate sites, and more. In contrast, the dark web refers specifically to sites that require special software to access.
2. Is accessing the dark web illegal?
Accessing the dark web itself is not illegal; however, many activities and content found there may be. It’s essential to stay within legal boundaries while exploring.
3. Can I access the dark web on my mobile device?
Yes, there are mobile versions of the Tor Browser available for both Android and iOS, allowing users to access the dark web on their smartphones.
4. What should I do if I encounter illegal activity?
If you come across illegal content, it’s advised to exit immediately and avoid any engagement. Reporting such activity to authorities is an option, though proceed with caution.
In conclusion, accessing the dark web can be both intriguing and risky. By following safety protocols and understanding what to expect, users can navigate this hidden part of the internet more securely. Always remember to practice caution and maintain awareness of potential dangers to ensure a safer experience online.