The Darknet represents a hidden realm of the internet, distinct from the surface web that most users are familiar with. It serves as a platform for various activities, both legal and illicit, operating through specific software that ensures anonymity. This article delves into the concept of adress darknet, exploring its significance, how it functions, and the associated risks and benefits.
- RAND Europe is an independent, not-for-profit research organisation whose mission is to help improve policy and decision-making through research and analysis.
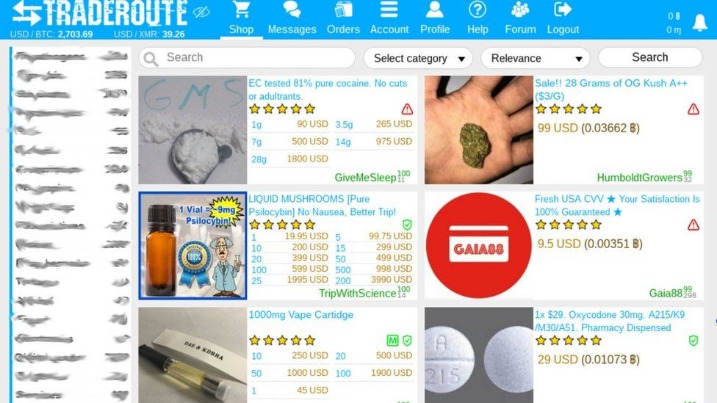
- Furthermore, all marketplaces accept forms of cryptocurrency, such as Bitcoin.
- This repository promotes responsible research and awareness.
- On 9 September 2015 ICANN, IANA and the IETF designated .onion as a 'special use domain', giving the domain an official status following a proposal from Jacob Appelbaum of the Tor Project and Facebook security engineer Alec Muffett.
- Tracing activity from a single address, we uncovered a network of 8 “seeder” wallets responsible for launching address poisoning attacks for this campaign.
WeTheNorth, often abbreviated as WTN, was launched to fill the void left by a previous Canadian market and has since grown steadily. However, BidenCash’s claim to fame or infamy was its freemium marketing approach. However, by mid 2025, BidenCash’s run came to an end when law enforcement seized its domains, delivering a major blow to the carding community. In its heyday 2022–early 2025, BidenCash became a significant platform for trading stolen credit card data and personal information. It has become one of the go to sites for buying compromised accounts and personal data in the cybercriminal world.
This combined model, that is, Deep Transfer Learning over Edge Computing(DTL-EC) will take the power of DL through DTL as well as would be applicable in critical sectors by EC to cope with a sudden pandemic. As mentioned in section 4.1.2, the DL has some limitations to cope with the challenges of a pandemic whereas Section 2.2 has described the task adaptability through DTL methods where data shortages are there. Data privacy and security also are considered ones of the big issues. Therefore, data of one region may not be effective to enhance knowledge in other regions.
Adress Darknet
The adress darknet is a subset of the Deep Web, where information and services are often encrypted and require specialized browsers, like Tor, to access. Here’s a look into its key aspects:
How Does the Darknet Work?

- Specialized Software: To access the darknet, users typically rely on Tor or I2P, which anonymize their location and identity.
- Hidden Services: Websites on the darknet often end with .onion (for Tor) or .i2p (for I2P), making them untraceable on standard web browsers.
- Encryption Protocols: Data transmitted on the darknet is encrypted to protect the privacy of users.
Benefits of the Darknet
- Privacy Protection: Users can communicate and browse anonymously, which is crucial for whistleblowers, journalists, and activists.
- Access to Restricted Information: In some countries, the darknet provides a platform for access to information that is censored on the surface web.
- Support Networks: Various communities form on the darknet, providing support and resources for those in need.
Risks Associated with the Darknet
While there are benefits to adress darknet, it is important to be aware of the risks involved:
- Illicit Activities: The darknet is notorious for illegal activities, such as drug trafficking, weapons sales, and hacking services.
- Scams and Fraud: Many scams exist on the darknet, targeting unsuspecting users looking for illicit goods or services.
- Exposure to Malware: Users may inadvertently download harmful software while navigating through darknet sites.
FAQs About the Darknet
What is the difference between the Deep Web and the Darknet?
The Deep Web encompasses all parts of the internet not indexed by search engines, while the darknet is a segment of the Deep Web that requires specific software to access.
Is it legal to use the Darknet?
Using the darknet is legal in many countries; however, engaging in illegal activities while on it is not.
What precautions should I take when accessing the Darknet?
- Stealer logs are packages of data stolen by malware from infected computers.
- Some data sources are listed in Table 5where COVID-19, as well as other pandemic data are available, so, researchers may use them for many purposes.
- Moreover, such facilities are usually high security and have several cameras recording activity 24/7.
- Before discussing the specific forums, it's essential to understand how these two environments differ in their fundamental structure, accessibility, and operational purpose.
- Can security teams legally monitor dark web forums for threat intelligence?
- Use a reliable VPN for additional anonymity.
- Only access known and reputable sites to minimize risks.
- Keep your software updated to avoid vulnerabilities.
In conclusion, the adress darknet offers a glimpse into a complex world that can serve various purposes, depending on the intentions of its users. While it can be a valuable tool for privacy and access to information, it is critical to approach it with caution and an understanding of the potential dangers involved.