Suspicious links can expose you to scams, malware, and other dark web dangers. Navigating the dark web is like starting an epic quest — it’s dangerous to go alone. Ben’s research focuses on digital infrastructures and how they become implicated in struggles over power and control; their PhD involved a four-year study of the Tor Project. Tor not only provides anonymity, but a hopeful vision of the Internet’s future, one in which these infrastructures of control may be less powerful than we might think. Tor is an attempt to seize back the possibility of a different future of the Internet—part of the long hacker history of utopian dreams of global community, resistance, and sharing of information.
The .onion dark web represents a unique and complex segment of the internet, hidden beneath the surface we commonly navigate. Accessible only through specific software like Tor (The Onion Router), the .onion domain offers a level of anonymity and privacy that eludes mainstream web users. This space is often associated with illicit activities, but it is essential to understand its multifaceted nature and the various communities that inhabit it.
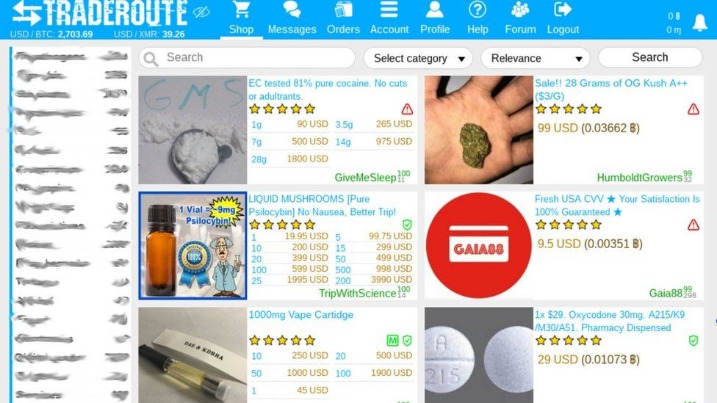
While the nature of the dark web has led to abuses and exploitations by bad actors, this underside of the internet is not illicit by nature. It also sells more than the illicit substances it's often known for, contraband can include stolen data, illegal firearms and exploitation material. For investigators, it can hold crucial information that would otherwise be inaccessible. In many countries, the dark web allows demonstrators to subvert authoritarian regimes and provides a free and open internet model that can evade censorship and provide privacy. Investigators should use non-attributable, isolated browsing with full auditing to reduce legal, security, and privacy risk.
It's difficult to provide an exact number of Tor users due to the anonymized nature of the network. Onion and com domains serve as top level domain identifiers for websites but they operate in very different environments and have distinct characteristics. A VPN encrypts your Internet traffic and routes it through a single secure server, hiding your IP address but still relying on the VPN provider's trust. However, they can't see what websites you're visiting, what you're doing inside Tor, or your final destination. The Tor network routes your Internet traffic through a series of at least three randomly selected nodes (an entry node, a relay node, and an exit node) before reaching its destination.
- If you’re interested in anonymous browsing, first check whether Tor, or even VPNs, are legal in your country.
- The Tor browser is perhaps the most popular dark web browser, but it’s not the only way to access the dark web.
- Whether you need data security, endpoint management or identity and access management (IAM) solutions, our experts are ready to work with you to achieve a strong security posture.
- The spider was started on lists of known onions like the Hidden Wiki and as onion pages seen in Recorded Future’s existing data holdings.
- While the Darknet can pose significant risks, including exposure to illegal content and cyber threats, it also provides a unique space for communities seeking anonymity.
onion Dark Web
The usage of the .onion domain stems from the desire for privacy and secure communication. Many users engage with this layer of the web to evade censorship, access restricted information, or communicate securely without fear of surveillance. The .onion dark web can be a refuge for activists, journalists, and whistleblowers who require anonymity to share sensitive information.
Accessing the .onion Dark Web
To access the .onion sites, users must download and install the Tor browser. This browser routes internet traffic through a network of volunteer Tor servers, obscuring user identities and locations. Once in the Tor network, users can visit .onion sites, which often have cryptic names. These names are generated to assure anonymity and privacy for both users and website operators.

Content on the .onion Dark Web
The content found on the .onion dark web ranges widely, from forums and marketplaces to blogs and news services. While some areas engage in illegal activities such as drug trafficking and weapon sales, others focus on legitimate discourse, privacy advocacy, or hosting whistleblowing platforms. For instance, popular sites include WikiLeaks, which operates in part on the .onion network to protect its sources.
Risks and Dangers
Exploring the .onion dark web comes with inherent risks. Users can encounter scams, malicious software, and illegal content that could lead to legal trouble. Moreover, the anonymity provided by Tor does not guarantee total safety; law enforcement agencies monitor .onion sites, and anyone engaging in illegal activities could still face serious repercussions. Caution and awareness are paramount for anyone delving into this hidden part of the internet.
The Future of the .onion Dark Web
As the digital landscape evolves, so does the .onion dark web. Emerging technologies and increasing concerns over privacy will likely shape its future development. With ongoing debates about internet freedom versus security, the .onion network may serve as a battleground for these critical issues, representing the fine line between a haven for free expression and a hub of illicit activities.
In conclusion, the .onion dark web is a complex environment that extends beyond its notorious reputation. While it does provide a platform for illegal transactions, it also plays a crucial role in safeguarding privacy and facilitating free speech in oppressive regions. Understanding its breadth and depth is essential for comprehending the modern internet landscape.