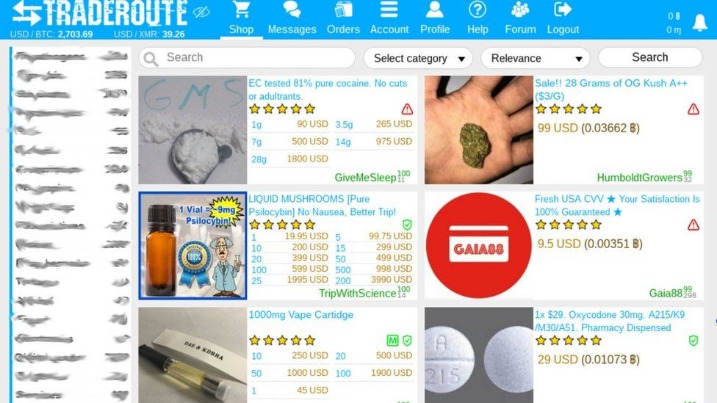
The rise of darknet markets has sparked a wave of interest and intrigue in the digital age. These elusive online platforms offer a range of goods and services that operate outside traditional regulatory frameworks. While they are often associated with illegal activities, the appeal of darknet markets extends beyond just illicit transactions. This article will explore the methods for accessing these hidden marketplaces, the risks involved, and the ethical considerations that come with their use.
- The experience is reminiscent of searching the web in the late 1990s.
- This would often result in the loss of data and trust, which in turn might encourage users to switch to competitor markets.
- ICE HSI takes a straightforward role in combating illegal activity on the Darknet.
- This content does not provide instructions or guidance on accessing the dark web.
- Your security program should include dark web monitoring as part of comprehensive threat intelligence.
Ransomware threat actors use malware to lock users out of their systems, demanding payment to restore access. Infostealer threat actors specialize in malware that harvests personal data without consent, such as login credentials, bank accounts, and social security numbers. As a hidden part of the Internet, the dark web is an ideal base for many cybercrime networks, hosting illegal marketplaces, anonymous forums, unethical software, and more. Black Ops Market is the future of darknet markets.
Now that there are organizations that employ trained and certified cybersecurity experts to detect vulnerabilities and gaps, hackers have other motivations. It used to be that technological advancements were the main factor that motivated hackers. Hackers have evolved over time, which has made defending cybercrime a challenging task. Understanding these motivations helps to plan effective cybersecurity strategies. For now, let’s go back in time by exploring the evolution of the dark web before looking at predictions for 2024 and beyond. Today’s biggest cyber threats aren’t exactly the same as they were yesterday or will be tomorrow.
Access Darknet Markets
Accessing darknet markets requires a series of steps that are crucial for maintaining privacy and security. The most common method of entry involves using a specialized browser known as Tor (The Onion Router). Tor allows users to browse anonymously by routing their internet traffic through multiple servers, obscuring their IP addresses.
Setting Up Tor
To start exploring darknet markets, users must first download and install the Tor browser. This process is relatively straightforward:
- Visit the official Tor Project website.
- Download the browser suitable for your operating system.
- Install the browser and launch it.
Finding Marketplaces
Once Tor is installed, users can begin searching for darknet markets. These marketplaces are often shared through forums, social media, and other platforms, but finding reliable sources can be challenging. It is essential to approach this carefully, as many links may lead to scams or malicious sites.
Ensuring Security
When accessing darknet markets, security should always be a priority. Here are several tips to consider:
- Use a VPN in conjunction with Tor for an added layer of security.
- Avoid sharing personal information to protect your identity.
- Be wary of offers that seem too good to be true; they often are.
Risks and Legal Implications
Engaging with darknet markets involves inherent risks, both legally and personally. Many goods sold on these platforms can breach laws in numerous jurisdictions, risking prosecution. Users must be aware of the potential legal consequences of their actions. Furthermore, the nature of transactions in darknet markets can expose buyers to scams and threats, making due diligence critical.
Ethical Considerations
Beyond the legal aspects, ethical questions arise regarding the use of darknet markets. Many individuals argue that these platforms facilitate illegal activities that could cause harm to individuals and society. Others contend that they provide a space for free expression and the exchange of information, especially in regions where such freedoms are restricted.
In summary, while accessing darknet markets is made possible through tools like Tor, the imperative to remain cautious and knowledgeable cannot be overstated. Users need to navigate this digital underworld with an acute awareness of the risks, legal implications, and ethical debates surrounding it. Ultimately, the choice to engage with darknet markets lies with the individual, but informed decisions are crucial in this unregulated space.