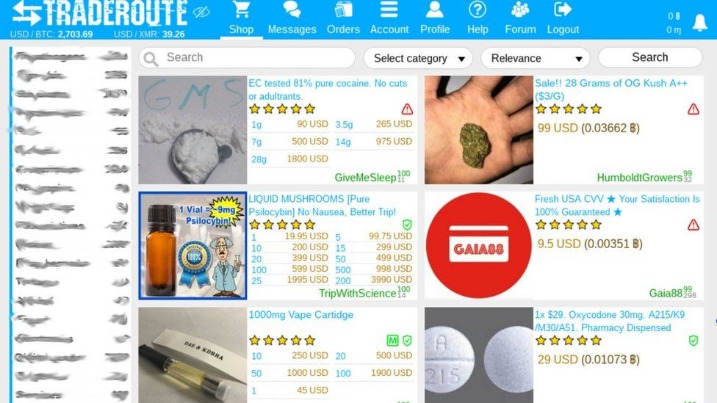
It was shut down by the FBI within two years and its founder Ross Ulbricht imprisoned for life, but multiple other darknet markets have since sprung up due to their enormous potential for illegal trading. This really shows the vast impact nations and organizations are facing due to the identity and PII information being stolen, bought, and sold in the darknet markets. Stolen identities are in big demand in darknet markets as they allow cybercriminals to conduct fraud using real identities of individuals who could have been victims to phishing/malware attacks or organizations holding PII data of their customers getting breached. This blog will not cover all the product types being available in the darknets but cover some of the most common types of information/ services which are transacted by cybercriminals in the darknet markets. It is also worth noting that not all digital data being sold in the darknet markets are gained from the result of successful cyber attacks.
The dark web has garnered significant attention over the years, often recognized for its association with illegal activities and anonymous transactions. Among its various sections, the darknet market stands out as a hub for the trade of illicit goods and services. Accessing darknet markets, however, is not as straightforward as visiting a typical e-commerce website. It requires specific tools and knowledge to navigate these hidden online spaces effectively.
Accessing Darknet Market
Before diving into the complexities of accessing darknet markets, it’s essential to understand the basic tools you'll need. The primary gateway to the dark web is the Tor browser, which allows users to browse anonymously. Downloading Tor is the first step for anyone looking to explore the darknet market.
For this reason, dark web monitoring is critical for security. The surface web, which is also called the visible web and the open web, is any website that search engines can add to their database. To access it at all, you need to use an anonymizing web browser such as “The Onion Router” (Tor) and a virtual private network (VPN). Altogether, this accounts for about 90% of the content of the internet, if not more. Simply put, the deep web is any part of the internet that is not indexed by search engines.
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. Russian Market makes this data instantly searchable and purchasable by anyone. Despite the legal interference, BriansClub still exists and continues to market credit card data and other sensitive information. It’s one of the largest dark web marketplaces, but you can also find it on the clear web. This was originally a forum, but shifted into a marketplace after users demanded Bitcoin payment options. The platform also uses 2FA, phishing warnings, and bug bounty programs to establish security around its services.
Installing the Tor Browser
To begin accessing darknet markets, you must first install the Tor browser. This browser is designed to route your connection through multiple servers, effectively masking your IP address and ensuring privacy. Once downloaded and installed, ensure you connect to the Tor network. This step is crucial as it enables access to .onion websites, where most darknet markets reside.
Finding the Right Market
- Since receiving Tor Project support in 2014, Ahmia has maintained dual access points through both clearnet and onion interfaces.
- This access layer allows global reach while limiting direct traceability.
- Figure 8 Scanned templates of Australian passports being listed at a darknet market
- They can simply purchase valid credentials from a marketplace vendor who aggregates stealer logs from thousands of infected devices.
After successfully installing Tor, the next challenge is locating trustworthy darknet markets. Many forums and websites provide wiki-type listings of available markets, but caution is necessary. Scams and dangerous sites abound, so it's wise to do thorough research before committing to any marketplace. Look for community reviews, user feedback, and consider using dedicated marketplaces that have a reputation for reliability.
Access Procedures and Security Measures
When you’ve found a suitable darknet market, navigating its interface may resemble standard online shopping experiences, but with unique precautions. Always access the market through a secure connection on the Tor network. Additionally, employing a reliable VPN can enhance your security by adding another layer of anonymity. This is particularly important as your activities on the darknet can attract unwanted attention.
Creating an Account
Most darknet markets will require you to create an account before you can make any purchases. During the registration process, it is advisable to use a pseudonym and not share personally identifiable information. This ensures that your true identity remains anonymous while you are accessing the darknet market. Moreover, enable two-factor authentication if available, as it helps in securing your account from unauthorized access.
Making Transactions Safely
When it comes to transactions on a darknet market, cryptocurrencies such as Bitcoin are commonly used. It is essential to have a digital wallet set up beforehand to facilitate these transactions. Additionally, be aware of the risks involved—buyer scams and product quality may not be guaranteed. Always read seller reviews and ratings before proceeding with any purchase.
Exiting Safely
After you’ve completed your transactions, knowing how to exit safely from the darknet market is just as important as accessing it. Ensure that you close the Tor browser completely. Consider clearing your browsing history and cache, and verify that no compromising information remains accessible on your device. Maintaining anonymity is critical when engaging with these types of online platforms.
Accessing darknet markets is not without its risks, but with the right precautions and tools, users can navigate these hidden marketplaces. Whether for legal purposes or illicit material, understanding how to safely access and utilize these networks is paramount in ensuring a secure experience.